Overview
Researchers have developed a technique that uses terahertz radiation to observe individual transistors switching inside a running CPU. The method can map data flow and operational patterns at the transistor level, a capability that goes far beyond traditional power analysis.
The technology has dual implications. For chip designers, it offers an unprecedented tool for debugging and performance optimization. For security, it introduces a new class of side-channel attack: physical data extraction through electromagnetic emissions from the processor itself.
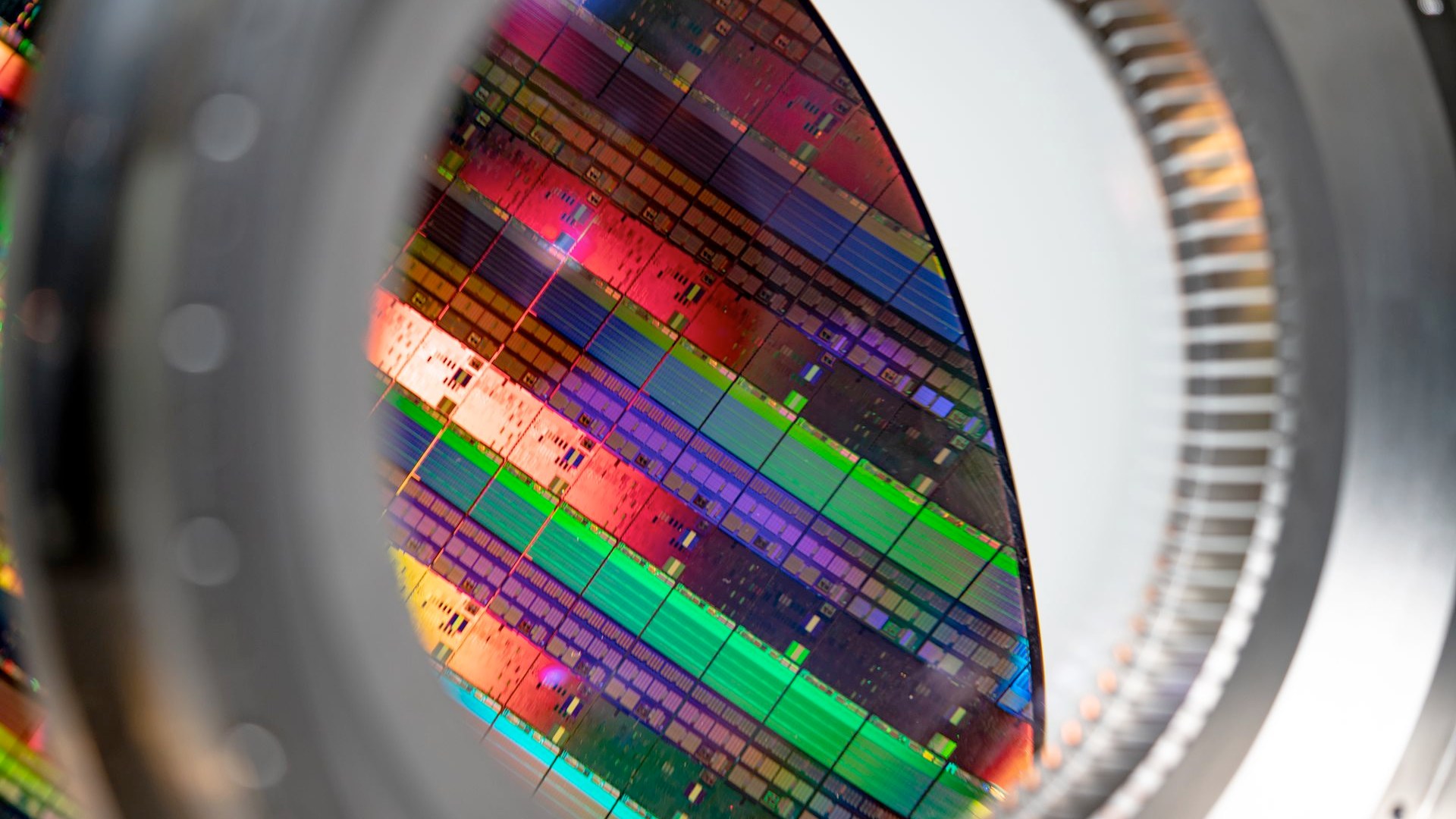
Visualizing the Invisible Silicon Core
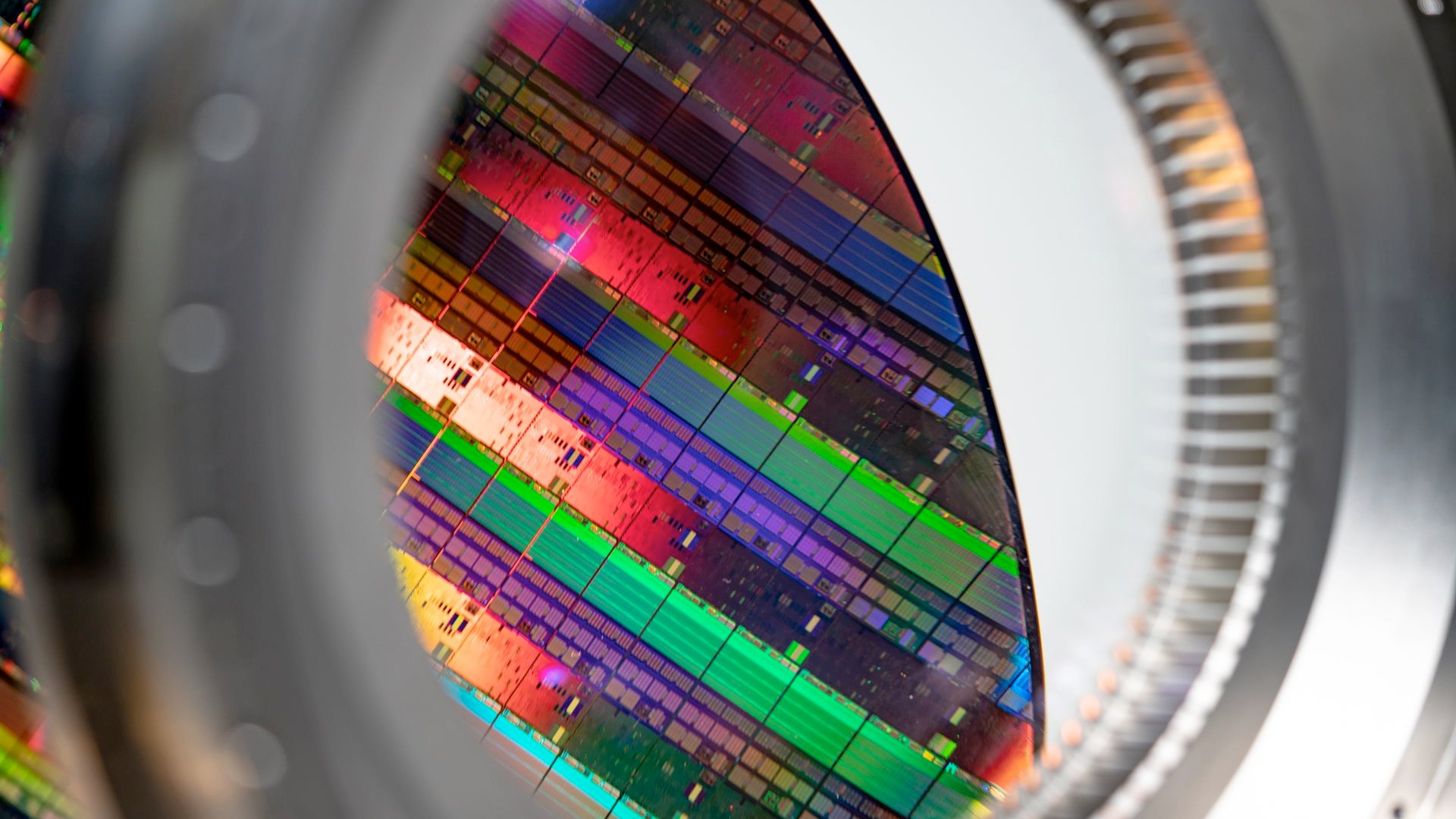
Visualizing the Invisible Silicon Core
The ability to observe transistor switching via terahertz radiation fundamentally changes how hardware engineers analyze chip performance. Historically, understanding data flow relied on indirect measurements, such as monitoring overall power draw or analyzing timing signals. These methods provide aggregated data, often obscuring the specific operations occurring at the gate level.
The THz approach, however, captures the transient electromagnetic fields generated by the physical movement of electrons within the transistors. Each logical operation—a 0 or a 1—creates a distinct, measurable electromagnetic fingerprint. This allows researchers to reconstruct the precise sequence of computations being executed, effectively visualizing the digital logic in real-time.
This deep visibility is crucial for the next generation of computing. As transistors continue to shrink and power density increases, understanding the physical interactions becomes paramount. The technique provides a non-invasive, high-resolution diagnostic tool, enabling manufacturers to optimize chip architecture and predict failure points with unprecedented accuracy.
The Terahertz Threat Model
The most immediate and concerning implication of this technology relates to data security. The very signals that allow researchers to observe the transistors also represent potential eavesdropping vectors. The electromagnetic radiation emitted during computation is not perfectly contained within the chip package.
This phenomenon establishes a tangible physical side-channel attack vector. Instead of needing physical access to the chip's internal bus lines, an attacker equipped with specialized THz receivers can potentially capture the unique radiation patterns associated with sensitive data processing. The data being processed—passwords, encryption keys, proprietary algorithms—is leaked as an unintentional electromagnetic byproduct.
Security experts warn that this raises the threat model from purely software-based attacks (like buffer overflows) to highly physical, remote attacks. The attacker does not need to compromise the operating system; they only need to detect the specific THz signature corresponding to the secret data being handled. This forces a re-evaluation of traditional hardware security measures.
Implications for Chip Design and Security Protocols
The existence of this THz leakage pathway mandates a fundamental shift in how processors are designed and hardened. Current security measures often focus on software obfuscation or physical tamper detection, but these are insufficient against a dedicated electromagnetic side-channel attack.
Future CPU architectures must incorporate advanced physical countermeasures. These could include specialized shielding layers, randomized signal noise injection, or dynamic power management techniques designed specifically to flatten the electromagnetic signature. The goal is to make the computational process appear electromagnetically uniform, regardless of the data being processed.
Furthermore, the research highlights the need for standardized, industry-wide protocols for hardware security auditing. If THz monitoring becomes commonplace, it will necessitate the development of certified "secure-by-design" benchmarks, ensuring that new chips meet minimum standards of electromagnetic emission control. This is not merely an academic problem; it is a looming commercial and national security concern.