Overview
The download page for CPUID, a highly trusted resource for processor and PC component information, was recently compromised, posing a direct threat to users seeking legitimate system diagnostics. Attackers successfully replaced the standard links for popular tools with malicious files, creating a sophisticated malware distribution vector. The incident serves as a stark reminder that even industry-standard, authoritative tech sites are susceptible to digital infiltration.
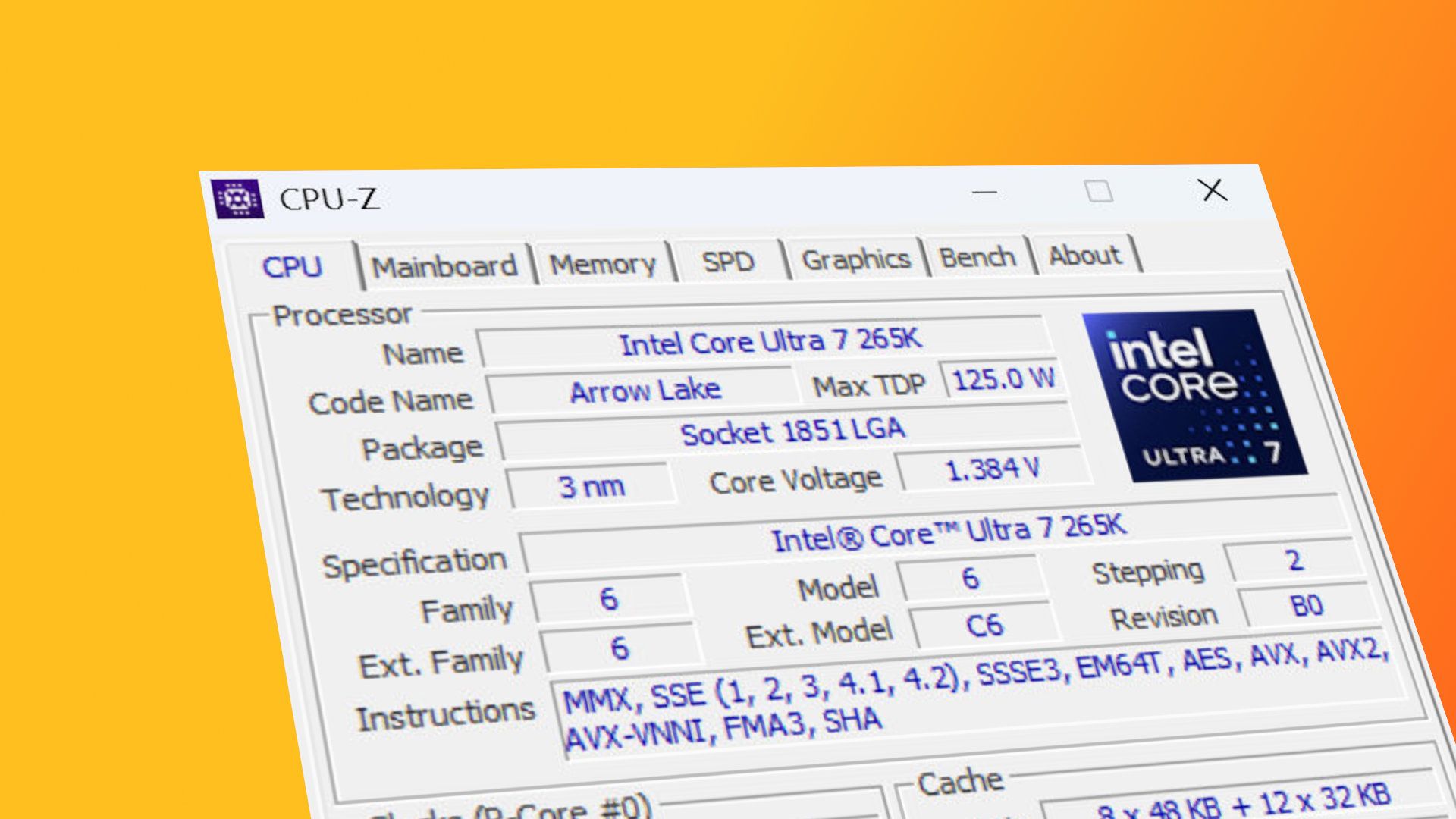
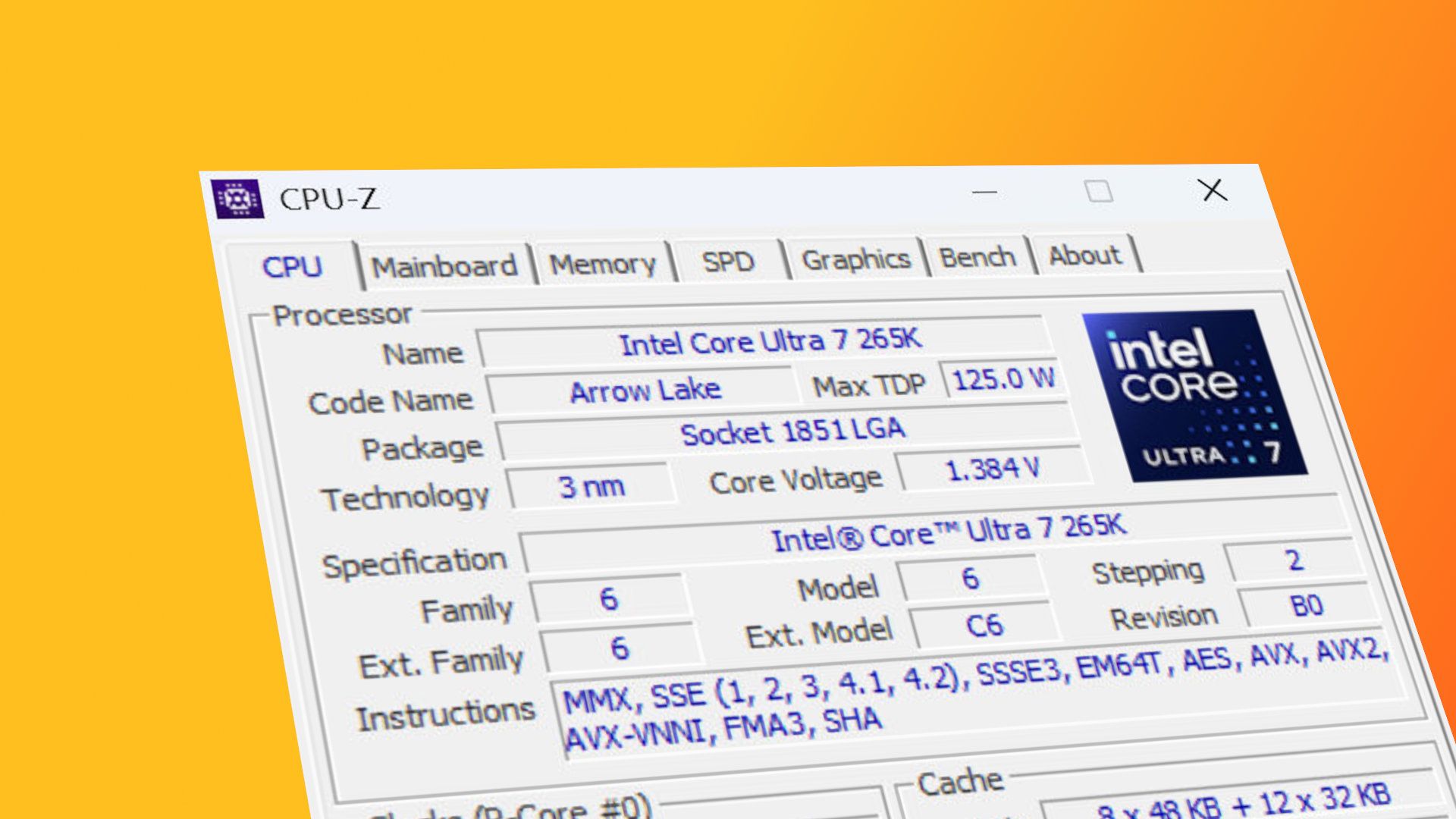
The specific tools, including those used for detailed processor identification and comprehensive PC hardware diagnostics, were the targets of the breach. Instead of the expected, functional software, users who visited the compromised page were directed to files containing malicious code. While the site owners quickly identified and patched the vulnerability, the window of exposure presented a significant risk to the global user base.
This breach underscores a persistent and growing threat landscape: the exploitation of trust. Tech sites like CPUID rely heavily on user trust, making their download portals prime targets for criminal elements looking to distribute malware at scale. The rapid detection and remediation by the site’s team, while necessary, only mitigates the immediate threat, leaving the industry to grapple with the underlying systemic vulnerabilities.
The Mechanics of the Compromise
The Mechanics of the Compromise
The attack did not involve a simple defacement; it was a targeted manipulation of the core functionality of the download page. The objective was to maintain the illusion of legitimacy while redirecting traffic to malicious payloads. This level of compromise requires deep access to the site's backend infrastructure, suggesting a sophisticated and well-resourced threat actor.
The tools at the center of the attack—the processor identification software and the general PC information utilities—are foundational resources for system builders, troubleshooters, and hardware enthusiasts. Their compromised status meant that users, believing they were downloading essential diagnostic software, were instead unknowingly installing malware. This mechanism is far more effective than simple pop-up scams, as it leverages the user's intent and the established trust associated with the brand.
The immediate fix confirmed that the malicious links were successfully removed and the site's integrity restored. However, the incident provides valuable data points for cybersecurity researchers and developers. It confirms that the threat model for major tech resource sites must account for persistent, deep-level backend infiltration, rather than just surface-level hacking attempts.
Supply Chain Risk and Trust Erosion
This event is a textbook example of a supply chain attack vector. The compromise of a single, high-traffic download portal allows attackers to bypass many traditional security measures because the victim is already operating within a trusted digital environment. The trust model that underpins the entire tech industry—the assumption that a major, established site is safe—is what the attackers exploited.
The implications extend beyond CPUID itself. Any website that serves as a primary download hub for critical, functional software is inherently vulnerable. Malware distribution through trusted channels is exponentially more dangerous than direct phishing emails because the user has already taken the step of navigating to what appears to be a safe, legitimate source.
Security professionals are increasingly recognizing that the focus must shift from merely securing the perimeter (the website's edge) to securing the entire operational environment, including the content management systems, the hosting infrastructure, and the deployment pipelines. The cost of maintaining this level of security is immense, and the failure to do so can result in catastrophic loss of user trust, as demonstrated here.
Hardening the Tech Download Ecosystem
For the industry to recover from incidents like this, several systemic changes are necessary. Developers and site owners must implement advanced Content Security Policies (CSP) and utilize multi-factor authentication across all administrative accounts. Simple passwords or single-layer security are insufficient when the value of the compromised data is high enough to warrant a sophisticated attack.
Furthermore, the community needs better tools for real-time monitoring of site integrity. Beyond standard DDoS protection, sites require dedicated security monitoring that actively checks for unauthorized changes to core assets, such as download links or embedded scripts. The speed of the fix was commendable, but the ability to prevent the initial compromise remains the critical, unsolved challenge.
For the end-user, the lesson is clear: even when visiting highly reputable sites, caution must remain paramount. Verifying the source of software downloads through multiple channels or utilizing dedicated, isolated virtual environments for testing unknown executables should become standard practice. The sophistication of the attack demands an equally sophisticated level of user vigilance.