Overview
ShinyHunters, the hacking collective responsible for breaching Rockstar Games’ digital infrastructure, has released its stolen data onto the public internet after the developer reportedly declined to meet a ransom demand. The data dump occurred on April 13, days ahead of the previously established deadline, confirming the severity of the breach. The leaked files, sourced via an exploit targeting a third-party cloud server metrics provider, contain detailed operational and financial metrics for Rockstar's major online titles.
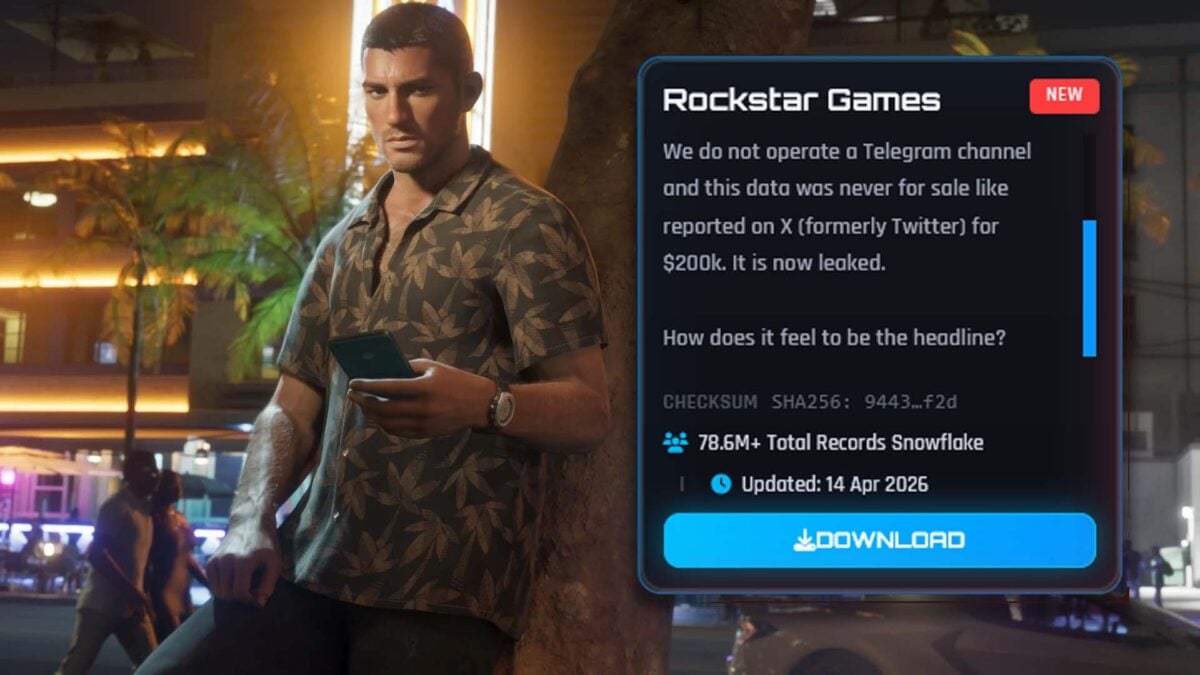
The release included a direct taunt to Rockstar Games, clarifying that the data was not for sale on platforms like Telegram, contrary to earlier reports. Instead, the group confirmed the compromise of Snowflake instances metrics data, linking the breach to Anodot.com. While the initial reports caused significant alarm, the actual contents of the leak suggest a focus on financial telemetry rather than the highly anticipated source code or proprietary assets of Grand Theft Auto VI.
Rockstar Games had previously acknowledged a data breach on April 11, characterizing the incident as the leak of a "limited amount of non-material company information." The current leak, however, moves beyond simple confirmation, providing specific, actionable data points that reveal the financial health and operational patterns of the company’s existing online ecosystems.
The Scope of the Financial Leak

The Scope of the Financial Leak
The released data primarily consists of metrics related to the operational performance of GTA Online and Red Dead Online. According to analyses of the leaked files, the metrics detail daily and weekly revenue streams, providing a granular view of how the titles are generating income. This level of financial telemetry is rarely made public and offers a comprehensive snapshot of the games' economic performance.
The data set reportedly includes breakdowns of spending habits across specific global markets. This suggests that the breach went beyond simple server uptime monitoring; it accessed deep business intelligence concerning consumer spending patterns and the monetary flow within the game economies. For industry analysts, such metrics are invaluable, offering a real-time, albeit illicit, look into the sustained profitability of Rockstar's core intellectual property.
The nature of the exploit itself is telling. The breach did not appear to originate from a direct infiltration of Rockstar's internal network or core development servers. Instead, the attack vector leveraged a vulnerability within a third-party service—specifically, a cloud server metrics provider. This highlights a critical, often overlooked vulnerability point in modern corporate IT architecture: the supply chain risk inherent in outsourced monitoring and analytics tools.
Implications for Rockstar’s Business Intelligence
The immediate implication of the leak is the exposure of proprietary business intelligence. While the absence of GTA VI source code files or player personal data may initially seem like a relief, the leakage of financial metrics poses a distinct, long-term threat. Competitors and market analysts can now track the economic pulse of Rockstar’s online operations with unprecedented clarity.
The data allows for the construction of sophisticated financial models based on real-world spending habits. For example, tracking the spending differential between GTA Online and Red Dead Online can inform decisions about cross-promotion, monetization strategies, or even resource allocation for future titles. The information is not just a headline; it is a playbook for understanding the revenue engine that powers the company.
Furthermore, the confirmed access to metrics data related to specific countries' spending habits provides geopolitical economic context. This suggests that the value of the leak lies not just in the raw numbers, but in the ability to segment and analyze regional consumer behavior, a highly valuable asset in the modern gaming market.
The Vulnerability of Third-Party Cloud Infrastructure
The incident underscores a growing systemic risk within the tech and gaming industries: reliance on interconnected, third-party cloud services. The fact that the exploit targeted a metrics provider, rather than the core game servers, shifts the focus of security concerns from perimeter defense to vendor risk management.
Modern game development and live service operations are inherently distributed, relying on dozens of external services for everything from analytics to payment processing. Each integration point represents a potential weak link. The ShinyHunters breach serves as a stark reminder that the most secure internal systems can be compromised by exploiting a seemingly innocuous external monitoring tool.
This situation forces a re-evaluation of how major studios manage their digital footprint. Security protocols must evolve beyond simple firewalls and must incorporate rigorous, continuous auditing of every single vendor and API connection. The cost of this negligence, as demonstrated by the leak, is measured in proprietary financial data and market confidence.